Microsoft has created other implementations of .NET to help resolve this. Mono is a free and open-source project designed to provide compatibility between .NET applications and other platforms, especially Linux. The .NET Core implementation is also free and open-source framework designed to bring lightweight, modular apps to multiple platforms.
- This often results in DLL files being left on your system, recreating the malicious program upon a reboot.
- This is also a great place to see the overwhelming amount of personal data other apps may have access to.
- All updates — from security updates and Windows Defender definition updates to optional updates and driver updates — will be installed automatically.
However, this feature can be misused when you share your PC with minors or kids. If you don’t want private browsing in Microsoft Edge then you can use the steps described below to block access to InPrivate mode in Edge. I’m sure you’re wondering why one would disable InPrivate Mode? A system administrator in a business, school, or similar location might block access to certain websites that a user could circumvent using incognito mode. Unlike the Group Policy method for the legacy version, this one will require new policy files for the new Microsoft Edge. The default policy settings will not work for the new Edge browser. It is easier to configure dsetup.dll download Windows 11 settings in Group Policy, but this one requires a few extra steps than the Registry Editor method.
Quickbooks https://rocketdrivers.com/dll/mso_dll Desktop Pro 2022 Upgrade
Follow the instructions on the screen to complete uninstallation and restart the computer. Synaptics is a company that makes pointing devices that are built into a wide range of laptop models and brands. You shouldn’t remove the device or its driver; if you do, your pointing device may stop working. Drivers are the connection between devices and your computer’s operating system.
- To make sure they’re applied, they now count as security updates and have a severity rating of Critical.
- Whaling refers to spear phishing attacks directed specifically at senior executives and other high-profile targets.
- Unlike the aggressive marketing push in 2015, the latest notification will be temporary and users can easily dismiss it.
- As such, the adoption of Vista in comparison to XP remained somewhat low.
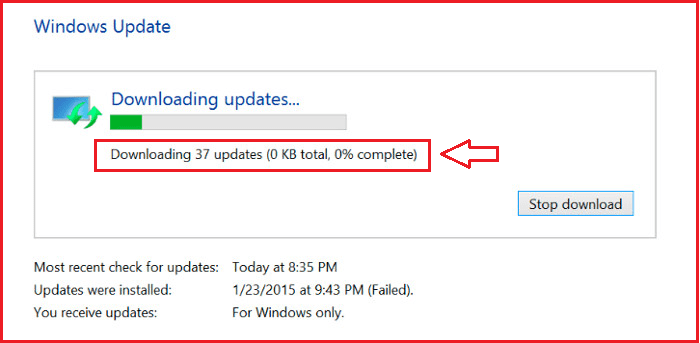
Alternatively, you can use the device manager to check if there are problems with any of your hardware devices. Since the support for Windows 7 has reached EOL and the last quality update has been released, Microsoft really wants consumers to know that it’s time for an upgrade. To download the last update on Windows 7, just open Control Panel and then choose Windows Update. Select ‘Check for updates’ to check for new updates if you don’t see this particular patch listed on the screen.
Root Aspects Of Dll – An Introduction
One of the simplest forms of page hijacking involves altering a webpage to contain a malicious inline frame which can allow an exploit kit to load. Page hijacking is frequently used in tandem with a watering hole attack on corporate entities in order to compromise targets.
Although page content may break in some cases, it may be a small price to pay to enjoy even more privacy. Go to the end of the text, tap space, then enter -inprivate . You can perform the basic Microsoft Edge security policytroubleshootingfrom theMEM admin center portal.One example is given belowHow To Start Troubleshooting Intune Issuesfrom theserver-side. The next level of troubleshooting is withMDM Diagnostics Toolto collect the log and information from theclient-side. Allow extensions you’ve given permission to run while browsing InPrivate.

